When Engineers Lose Visibility: The Hidden Operational Risk of Centralized Network Dependencies
Why Control Planes Fail When They Depend on the Networks They Manage
In today’s enterprise, service provider, and federal environments, centralized management platforms have become the operational standard. Network monitoring tools, orchestration layers, and remote access frameworks promise efficiency, automation, and unified control.
But beneath that efficiency lies a critical architectural flaw.
Most centralized management systems depend entirely on the very networks they are designed to manage.
And when those networks fail, so does visibility.
The Illusion of Continuous Visibility
Modern infrastructure assumes persistent connectivity.
Dashboards are expected to remain online. Alerts are expected to trigger. Remote access is expected to function. Engineers operate under the belief that if something goes wrong, they will be able to see it, access it, and fix it.
That assumption is increasingly dangerous.
Because when the network degrades, centralized visibility does not degrade gracefully. It collapses.
How Visibility Loss Happens in Real Environments
Operational failure rarely occurs as a single event. It unfolds in stages, each one reducing an organization’s ability to respond effectively.
1. Degradation
Intermittent connectivity begins to impact monitoring tools and management platforms. Alerts become inconsistent. Data becomes incomplete. Engineers begin troubleshooting with partial information.
2. Isolation
Devices and sites fall out of management systems entirely. Remote access becomes unreliable or fails altogether. Control is fragmented, and response efforts slow.
3. Blindness
At this stage, the organization has lost visibility into critical infrastructure. There is no remote access, no telemetry, and no ability to diagnose or remediate issues from centralized systems.
This is where outages escalate into operational crises.
The Real Risk: Loss of Control, Not Just Downtime
Most organizations measure outages in terms of availability or uptime.
But the most damaging failures are not defined by downtime alone.
They are defined by the loss of control.
When engineers cannot access devices, cannot validate system state, and cannot execute recovery actions, even minor incidents can escalate into prolonged disruptions.
In these scenarios, recovery becomes manual, slow, and often dependent on physical intervention.
The Single Point of Failure Built Into Modern Architectures
Centralized management architectures create an inherent dependency loop:
You need the network to manage the network.
This creates a single point of failure at the control plane level.
Whether caused by:
Network misconfigurations
Software or firmware failures
Carrier outages
Power events
Cyber incidents targeting management access
The result is the same: the management layer becomes unreachable when it is needed most.
Why Traditional Remote Access Does Not Solve the Problem
Many organizations attempt to mitigate this risk using VPNs, bastion hosts, or Zero Trust access platforms.
These approaches improve security posture, but they do not eliminate dependency.
They still require:
If the network is unavailable or compromised, these access methods fail alongside it.
They are extensions of the production network, not alternatives to it.
Out-of-Band Management: Designing for Independence
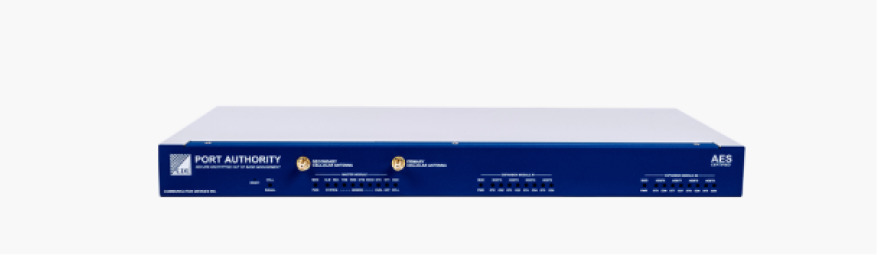
Out-of-Band Management (OOBM) fundamentally changes the architecture.
Instead of relying on the production network, OOBM establishes an independent, physically and logically separate access path to infrastructure.
This path remains available regardless of the state of the primary network.
With a properly designed OOBM architecture, organizations gain:
Persistent Access: Direct console-level connectivity to devices even during total network outages
Operational Isolation: Separation from production traffic and attack surfaces
Deterministic Recovery: The ability to diagnose and remediate issues without dependency on the affected network
Reduced MTTR: Faster incident response and resolution
In federal and critical infrastructure environments, OOBM is increasingly treated not as a convenience—but as a requirement.
OOBM as a Security Control Plane
The role of OOBM has evolved.
It is no longer just a recovery tool for network failures.
It is now a critical component of secure access architecture.
In environments aligned with Zero Trust principles and federal mandates, OOBM provides:
A hardened, controlled pathway for privileged access
Support for strong authentication mechanisms, including offline 2FA
Isolation of management traffic from production threats
Compliance alignment with frameworks such as FISMA and FIPS 140-3
This positions OOBM as a true control plane—separate, secure, and resilient.
Operational Resilience Is an Architectural Decision
Resilience is not achieved through monitoring tools or response playbooks alone.
It is designed into the architecture.
Organizations that rely solely on centralized, in-band management are implicitly accepting risk:
The risk that when something breaks, they may not be able to see it.
The risk that when they need access most, it will not be available.
The risk that recovery will depend on conditions they cannot control.
Out-of-Band Management removes that uncertainty.
Conclusion: Ensuring Engineers Always Have a Way Back In
After decades of evolution in network architecture, one principle remains constant:
The most dangerous failure is not losing the network.
It is losing visibility and control of it.
Out-of-Band Management ensures that no matter the scenario—outage, misconfiguration, or cyber event—engineers retain the ability to access, diagnose, and recover infrastructure.
Because in mission-critical environments, control cannot be conditional.
It must be guaranteed.