Out-of-Band Architecture vs. Traditional Remote Access
Why VPNs and Jump Servers Cannot Replace True OOB Infrastructure
In modern enterprise and government environments, remote access is often treated as a solved problem.
VPNs are ubiquitous. Jump servers are considered best practice. Zero Trust architectures are rapidly becoming the standard framework for identity and access control.
On paper, these approaches appear comprehensive.
In reality, they share a critical flaw.
They all depend on the very network they are meant to manage.
And when that network fails—or worse, is compromised—these tools frequently become inaccessible, ineffective, or part of the attack surface itself.
This is where Out-of-Band Management (OOBM) fundamentally changes the equation.
OOB is not simply another remote access method. It is a distinct architectural layer designed to maintain control when everything else breaks.
The Core Architectural Divide
At the heart of the issue is a simple but often overlooked distinction: dependency.
Traditional Remote Access (VPNs and Jump Servers)
Traditional remote access solutions operate in-band, meaning they rely on the production network to function.
They depend on:
Routing and switching infrastructure
Firewall policies and segmentation
DNS resolution
Authentication services such as Active Directory, LDAP, or cloud identity providers
Access is granted only after successfully traversing the same network that may be degraded, misconfigured, or under attack.
Out-of-Band Management (OOB)
Out-of-Band Management operates on a completely separate management plane—both physically and logically.
It is characterized by:
Independent transport paths (cellular, dedicated management networks, or isolated links)
Serial console access to critical infrastructure
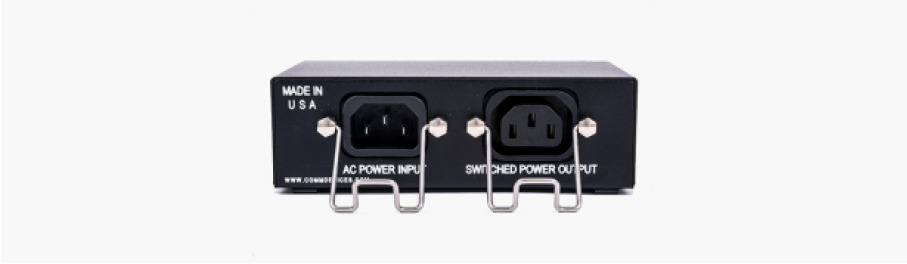
Direct device-level control, including power management
Secure access mechanisms embedded within the OOB infrastructure itself
This separation is not a feature. It is the foundation.
If your access path depends on the system you are trying to fix, you do not have control.
Where VPNs and Jump Servers Break Down
Traditional remote access solutions perform well under normal operating conditions. They are not designed for failure scenarios, which is precisely when control matters most.
1. Dependency on Network Availability
When core infrastructure fails, access disappears.
A routing issue, firewall misconfiguration, or control plane failure can:
At that point, recovery requires physical intervention—or an independent access path.
2. Expanded and Shared Attack Surface
VPNs and jump servers extend the attack surface into the management plane.
Once an attacker gains access:
Lateral movement becomes easier
Privileged systems are exposed through shared infrastructure
Management interfaces become reachable through compromised pathways
In modern breach scenarios, attackers specifically target management access because it provides leverage over the entire environment.
3. Authentication Stack Fragility
Traditional access methods rely heavily on centralized identity systems.
If identity services are:
Misconfigured
Unavailable
Compromised
Then administrative access may be delayed or completely blocked.
This creates a dangerous paradox: the systems required to authenticate access are often the same systems impacted during an incident.
4. Lack of Direct Device Control
VPN and jump server access typically operates at the network or OS level.
They do not provide:
Without these capabilities, recovery is limited, slow, and often requires on-site intervention.
Out-of-Band Management: Control Without Dependency
Out-of-Band architecture is purpose-built for the conditions where traditional access fails.
Security Embedded at the Infrastructure Layer
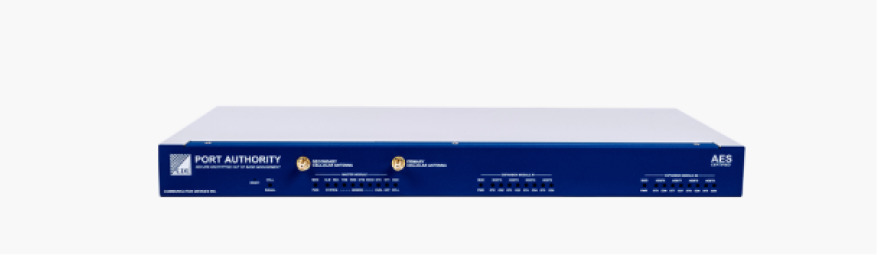
CDI’s approach to OOBM is not dependent on external systems to establish trust.
Security is enforced within the connection itself through:
Cryptographic controls operating inside validated boundaries
Key-based authentication models
Hardened access paths that do not rely on upstream identity infrastructure
This ensures access remains available—even when identity systems are degraded or offline.
Operational Independence
OOB infrastructure functions independently of:
This independence is what allows organizations to maintain command and control during outages, misconfigurations, or active security incidents.
Integration Without Fragility
CDI solutions integrate with existing security ecosystems, including:
However, these integrations enhance visibility—they do not define access. Control remains intact regardless of the state of the broader security stack.
Where Traditional Remote Access Still Fits
VPNs and jump servers are not obsolete. They are effective for:
But they are not designed to serve as the last line of control. That role belongs to Out-of-Band infrastructure.
The Strategic Takeaway
VPNs solve for access under normal conditions. Out-of-Band Management solves for control under failure and attack.
In a world defined by:
Increasing network complexity
Expanding attack surfaces
Zero Trust mandates
Mission-critical uptime requirements
Organizations must design for the moment when the primary network cannot be trusted. Because that moment is no longer hypothetical. The system you depend on for recovery cannot depend on the system that just failed.
Out-of-Band Management is not a backup strategy. It is the control plane that ensures you are never locked out of your own infrastructure.