Fortify Your Network: Why "Made in the USA" Means Secure Solutions

Adam Cady

There’s no doubt that malicious state actors are actively trying to penetrate your sensitive networks. In this environment, the provenance of your network security solutions can make the difference between safeguarding your data and inadvertently exposing it to prying eyes. As global corporations and governments increasingly blacklist products from regions known for aggressive data mining, the importance of choosing technology that is “Made in the USA” becomes strikingly clear. It’s not just about patriotism or supporting local industries; it’s about securing a trusted shield for your digital infrastructure.
While some may dismiss the origin of manufacturing as irrelevant, for organizations focused on preserving the sanctity of their data, this distinction is paramount. Imagine a fortress built with walls so strong that even the most cunning adversaries cannot breach them. That’s precisely what American-made network solutions offer—a defense born from a commitment to privacy and ethical manufacturing practices. The United States, with its robust intellectual property rights framework and dedication to personal freedoms, ensures that products made on its soil prioritize user privacy. Companies like CDI exemplify this ethos by incorporating advanced security protocols, such as FIPS 140-3 validation, into every product they produce.
By examining the specifics of network security, it becomes clear that "Made in the USA" is synonymous with secure solutions. In this landscape, integrity and innovation are not just buzzwords; they are the foundational elements of trust.
The Impact of Digital Espionage on Network Security
Digital espionage has emerged as a pervasive threat in today’s interconnected world. Cybercriminals and state-sponsored hackers are continually seeking ways to infiltrate networks and gain unauthorized access to sensitive data. The consequences of such breaches can be devastating, ranging from financial losses to reputational damage. To combat this growing threat, organizations must prioritize network security and invest in robust solutions that can withstand increasingly sophisticated attacks.
A key factor in network security is the provenance of the technology being used. The origin of a product plays a significant role in determining its trustworthiness and integrity. In an era where data mining practices have sparked global concerns, choosing technology that is "Made in the USA" offers distinct advantages.
Global Concerns Over Data Mining Practices
Data mining involves the extraction and analysis of large volumes of data to uncover patterns, trends, and insights. While it can be beneficial for businesses and research, data mining also raises serious privacy concerns. Many countries have implemented regulations to protect individuals' personal data from being exploited without their consent. China, in particular, has faced significant scrutiny for its data mining practices and alleged state-sponsored cyber espionage activities. The Chinese government’s history of seizing intellectual property (IP) from foreign products has created an atmosphere of insecurity among global governments and corporations. This culture of "what’s yours is mine" heightens concerns about relying on technology sourced from certain regions.
The Significance of Provenance in Network Security Solutions
When it comes to sensitive network security products, where and how a product is manufactured is of critical importance. Choosing solutions that are "Made in the USA" signifies more than just support for local industries or an expression of patriotism; it represents a commitment to integrity. The United States has long championed privacy and liberty, and this ethos is reflected in products manufactured within its borders. By opting for American-made network security solutions, organizations can trust that their rights to privacy will be respected. The strong intellectual property rights framework in the USA ensures that these products prioritize user privacy and data protection.
Advantages of Choosing "Made in the USA" Technology
Opting for technology that is "Made in the USA" offers several advantages regarding network security:
1. Enhanced Data Privacy: American-made solutions are designed to protect user data. The stringent regulations and standards governing data privacy in the USA ensure that these solutions provide a higher level of protection against unauthorized access.
2. Ethical Manufacturing Practices: The manufacturing processes employed in the USA adhere to strict ethical guidelines, ensuring that products are not compromised during production or tampered with by malicious actors.
3. Trust and Reliability: American-made technology has gained a reputation for its reliability and trustworthiness. Organizations can have confidence in the quality and effectiveness of these solutions when it comes to safeguarding their networks.
Ensuring Data Privacy Through Ethical Manufacturing Practices
Data privacy extends beyond just software or encryption protocols; it encompasses every stage of a product’s lifecycle, including its manufacturing process. Ethical manufacturing practices play a crucial role in ensuring that network security solutions remain uncompromised from inception to deployment. "Made in the USA" technology undergoes rigorous quality control measures throughout its production cycle, minimizing the risk of vulnerabilities or backdoors being introduced into the final product. By choosing such solutions, organizations can have peace of mind knowing their network security infrastructure is built on a foundation of integrity.
CDI: A Case Study in Secure Network Solutions
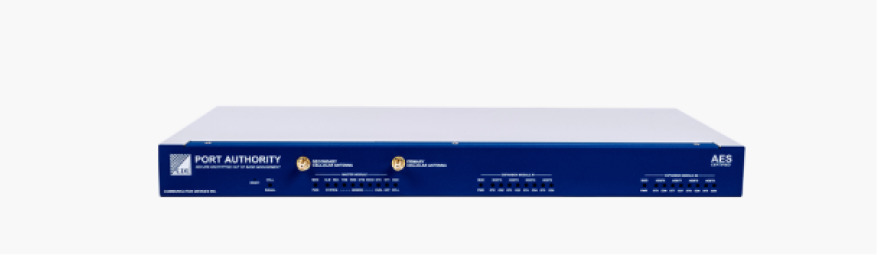
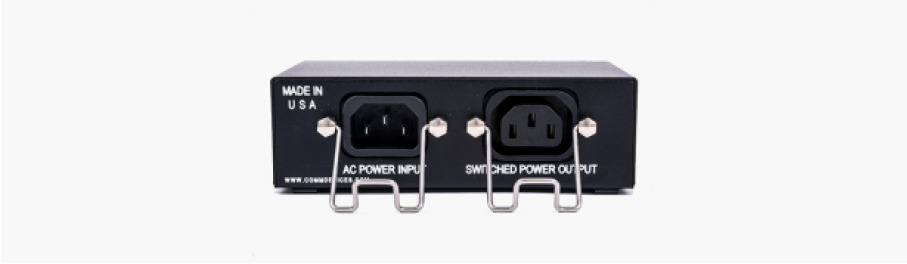
One notable example of a company that exemplifies the advantages of "Made in the USA" technology is CDI. With a history dating back to 1976, CDI has been at the forefront of producing secure network solutions for government and global industries.Unlike many competitors who outsource manufacturing overseas, CDI proudly designs, builds, and supports its products within the United States. This commitment to local production ensures that every aspect of the manufacturing process adheres to stringent quality control measures and ethical guidelines.
Integrating FIPS Validation for Enhanced Security
In addition to being "Made in the USA," CDI's network security solutions stand out due to their integration of Federal Information Processing Standards (FIPS) validation. FIPS 140-3 Validation is a critical accreditation that ensures products meet stringent security requirements set by the U.S. government.FIPS validation provides organizations with an added layer of assurance that their network security solutions have undergone rigorous testing and meet industry-leading standards. CDI's commitment to FIPS 140-3 Validation sets them apart from competitors who may claim similar features but lack the necessary certifications.
Importance of Provenance in Network Security Solutions
The importance of provenance in network security solutions cannot be overstated. By choosing technology that is "Made in the USA," organizations can fortify their networks with secure solutions built on integrity, trust, and a commitment to user privacy.In an era where digital espionage poses significant threats, it is crucial to prioritize network security and invest in reliable products. By understanding the impact of digital espionage on network security and recognizing the advantages offered by "Made in the USA" technology, organizations can take proactive steps to safeguard their sensitive data and protect themselves from evolving cyber threats.
Related Tags
Made in USANetwork SecurityDigital EspionageFIPS ValidationData PrivacyState ActorsCDI SolutionsAmerican ManufacturingEthical PracticesTechnology ProvenanceCybersecurityData ProtectionNetwork IntegrityIP ProtectionGovernment SecurityEnterprise SolutionsManufacturing SecuritySupply Chain TrustPrivacy RightsNational SecurityFederal ComplianceData Mining ConcernsShare this article
Related Content
United States Office
- 85 Fulton Street Boonton, NJ 07005
- +1 973-334-1980
- +1 973-334-0545
- info@commdevices.com
© 2023 Communication Devices, Inc.